Amid a flurry of flashy announcements this week, Apple also unveiled a new security feature for its iPhone 17 and iPhone Air models, aimed at combating surveillance vendors and the vulnerabilities they frequently exploit.
The feature, called Memory Integrity Enforcement (MIE), actively blocks memory corruption bugs—one of the most commonly exploited flaws by spyware creators and forensic tool makers used by law enforcement.
Apple’s New Security Tackles Memory Exploits, Boosts iPhone Protection
“Mercenary spyware targeting iOS often shares the same core tactic as attacks on Windows and Android: exploiting memory safety issues, which are widespread, powerful, and industry-wide,” Apple explained in a blog post.
Cybersecurity experts — including those who develop hacking tools and iPhone exploits — told TechCrunch that Apple’s new security feature could make its latest iPhones among the most secure internet-connected devices available. This advancement is expected to significantly disrupt spyware makers and zero-day exploit developers who infect targets or extract their data.
“The iPhone 17 likely offers the most secure connected computing environment in existence,” said a security researcher with years of experience creating and selling zero-days and cyber tools to the U.S. government.
MIE Raises the Bar by Increasing Exploit Development Costs and Complexity
According to the researcher, the introduction of MIE will increase both the time and cost needed to develop exploits for these new devices, which will, in turn, drive up prices for their clients.
“This marks a major development,” said the researcher, who requested anonymity due to the sensitive nature of the topic. “It’s not completely unhackable, but it’s the closest we’ve come. Nothing is ever 100% secure, but this significantly raises the bar.”
Jiska Classen, a professor and iOS researcher at the Hasso Plattner Institute in Germany, agreed that MIE will increase the cost of developing surveillance tools.
MIE Renders Many Current Exploits Ineffective, Disrupting Spyware Vendors
According to Classen, this is because many of the bugs and exploits currently used by spyware companies and researchers will no longer function once the new iPhones launch with MIE in place.
“I can imagine that, for a period of time, some mercenary spyware vendors might not have functional exploits for the iPhone 17,” said Classen.
“This will make things significantly harder for them,” added Patrick Wardle, a security researcher and founder of a startup focused on Apple cybersecurity. “Though, it’s important to remember this is always a cat-and-mouse game.”
Wardle also recommended that anyone concerned about spyware attacks should consider upgrading to the latest iPhones.
Experts interviewed by TechCrunch said that MIE will weaken the effectiveness of both remote attacks—like those carried out using spyware such as NSO Group’s Pegasus or Paragon’s Graphite—and physical device hacks using tools like Cellebrite or GrayKey.
Targeting The “Bulk of Exploits”
Most modern devices, including most current iPhones, use software written in programming languages that are vulnerable to memory-related issues, often known as memory overflow or corruption bugs. When these bugs trigger, they allow data from one app’s memory to leak into other parts of the device where it shouldn’t be.
These memory bugs can enable hackers to access and control areas of a device’s memory that should be off-limits. This access can be exploited to install malicious code that gains wider control over a user’s data stored in the phone’s memory and then extract that data via the device’s internet connection.
Memory Integrity Enforcement (MIE) is designed to protect against these extensive memory attacks by significantly shrinking the potential areas where memory vulnerabilities can be exploited.
Halvar Flake, an offensive cybersecurity expert, stated that memory corruptions account for “the vast majority of exploits.”
Apple’s MIE: An Enhanced Memory Tagging Extension Built on Arm Technology
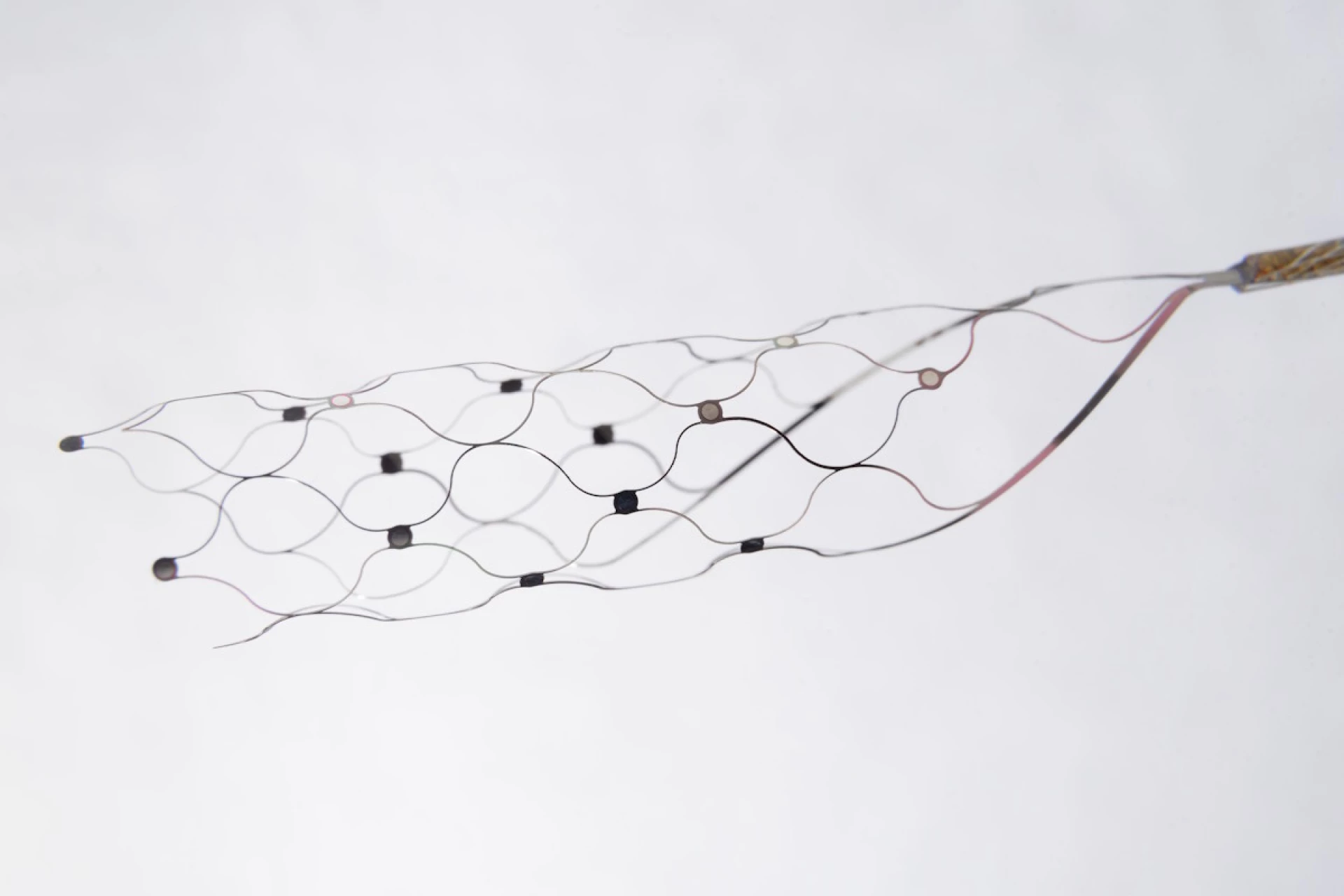
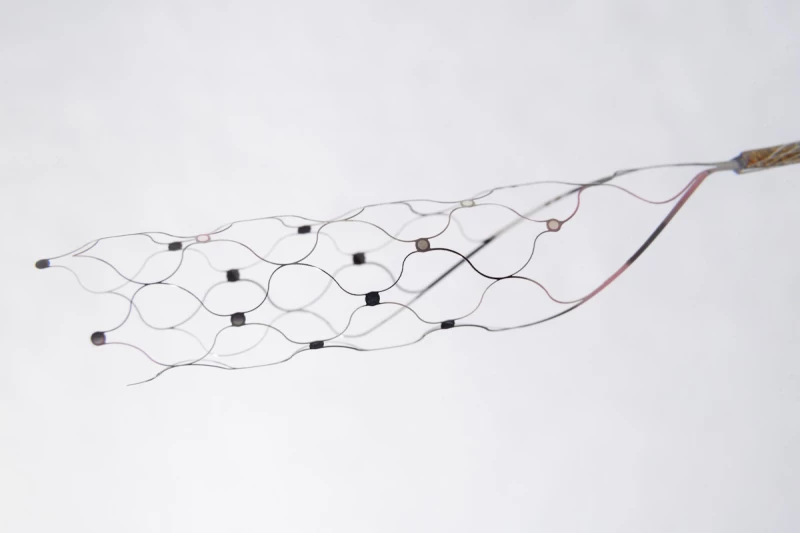
MIE is based on a technology called Memory Tagging Extension (MTE), originally created by chipmaker Arm. Apple revealed in a blog post that over the past five years, it collaborated with Arm to enhance and expand these memory safety features into what’s now called Enhanced Memory Tagging Extension (EMTE).
MIE is Apple’s version of this advanced security technology, leveraging the company’s unique ability to control its entire technology stack—from hardware to software—unlike many other phone manufacturers.
Google provides MTE support for some Android devices, and the security-focused GrapheneOS—a custom Android version—also includes MTE.
However, other experts believe Apple’s MIE goes beyond this. Flake noted that while the Pixel 8 and GrapheneOS are “almost comparable,” the new iPhones will be “the most secure mainstream” devices.
How MIE Protects Memory Access and Aids Attack Detection
MIE functions by assigning a unique secret tag—like a password—to each segment of memory on the newer iPhones. Only apps with the correct tag can access that memory. If the tag doesn’t match, the security system blocks the access, causes the app to crash, and records the incident.
The crash and log are especially important because spyware and zero-day exploits often cause crashes, making it easier for Apple and security researchers to detect attacks.
“A single mistake can cause a crash and create a potentially recoverable trace for defenders,” said Matthias Frielingsdorf, vice president of research at iVerify, a company that develops spyware protection apps. “Attackers already had strong reasons to avoid memory corruption.”
Apple did not respond to requests for comment.
MIE Default Protection for Apple Apps, Third-Party Adoption Needed for Broader Impact
MIE will be enabled by default across the system, protecting apps like Safari and iMessage, common targets for spyware. However, third-party apps will need to implement MIE themselves to enhance user protection. Apple has provided developers with a version of EMTE to facilitate this.
In short, MIE is a major positive advancement, but its full effect will take time to materialize, depending on developer adoption and how many users upgrade to new iPhones.
Some attackers will inevitably find ways to bypass it.
“MIE is definitely a positive development and could be a game-changer by raising the cost for attackers and possibly pushing some out of the market,” said Frielingsdorf. “However, many malicious actors will still manage to succeed and continue their operations.”
Read the original article on: Tech Crunch
Read more: Apple Unveils iPhone 17 Pro Featuring Significant Camera Improvements.